Automatic 4K/HD for Youtube extension pulled from Chrome Store for pop-up ad abuse
A popular browser extension has been removed by Google from the Chrome Web Store after it started spamming users with irritating pop-up advertisements.
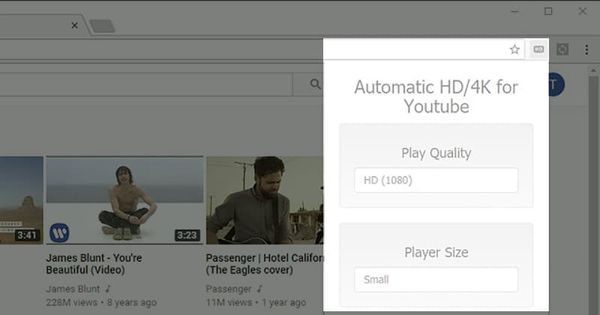
The “Automatic 4K/HD for Youtube” extension, used by over 4 million Chrome users to force YouTube into playing videos at high quality, was recently updated to display ads for another Chrome extension.
Ironically, as ZDNet describes, the Chrome extension it began to aggressively advertise was one that purported to be an ad-blocker.

The unwanted ads took advantage of Chrome”s desktop notification feature, in breach of Google’s developer policies.
Disgruntled users left poor reviews on the extension’s page on the Chrome Web Store, warning others who might be considering installing the code, and turned to social media as they attempted to discover the source of the unwanted ads.
Eventually they identified that the “Automatic 4K/HD for Youtube” extension was responsible for the nuisance pop-up ads.
The inevitable concern, whenever a browser extension begins to behave in an out-of-character fashion, is that it might have been hijacked by someone else with malicious intent.
In the past a number of browser extensions and plugins have either been purchased from their original creators (or even, in some cases, hijacked by hackers) who have seized the opportunity to behave maliciously on users’ desktops.
As I’ve described before, many people don”t recognise the potential security risk of browser extensions, because of the power they can have over the webpages you visit.
An ad blocker, for instance, can read and change all your data on any websites you land on. It has to have that ability to let it block website ads. When you install a browser extension, you”re placing a lot of trust in it never turning evil.
The threat of rogue extensions is not theoretical, but very real.
Late last year, for instance, researchers warned that a state-sponsored attack thought to have originated from North Korea was targeting academic institutions through a malicious browser extension called “Font Manager” in the Chrome Web Store.
And just last month, a fake “Flash Player” extension in the Chrome Web Store was found to be stealing payment card details entered in web forms.
Fortunately, in the case of “Automatic 4K/HD for Youtube” it doesn’t appear that it was planning anything outright malicious, but the aggressive pop-up ads have fallen foul of Google – which has now removed the offending extension from the Chrome Web Store.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







