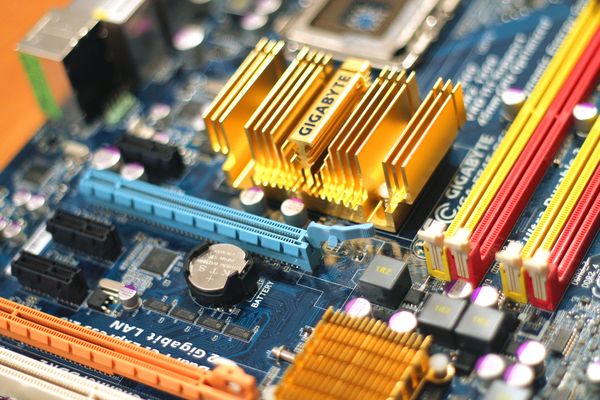
BIOS Vulnerability Targets Gigabyte Motherboards
A BIOS vulnerability that allows attackers to tamper with firmware on PCs could kill flash protection and secure boot, and even bypass Virtual Secure Mode on Windows 10 Enterprise.
Stating that at least four Gigabyte motherboards appear to be affected (Z68-UD3H, Z77X-UD5H, Z87MX-D3H, and Z97-D3H), researcher Dmytro Oleksiuk believes a lot more could be just as vulnerable to the exploit. The BIOS vulnerability in the System Management Mode (SMM) code is also believed to impact a number of Lenovo PCs, according to a Twitter post by Alex James.
“Proof of concept exploit for this vulnerability is designed as UEFI application that runs from UEFI shell,” reads the Github disclosure posted by Oleksiuk. “It’s also possible to exploit it from runing operating system but you have to implement your own EFI_BASE_PROTOCOL.Communicate() function.”
While Lenovo has already issued an advisory tagged with a high severity impact, it also stated that this is an uncoordinated disclosure and it”s investigating possible mitigation techniques. Although the code with the SMM vulnerability seems derived from a common code base provided by Intel, Lenovo did state that it”s actively investigating the issue.
“Importantly, because Lenovo did not develop the vulnerable SMM code and is still in the process of determining the identity of the original author, it does not know its originally intended purpose,” reads the Lenovo advisory. “But, as part of the ongoing investigation, Lenovo is engaging all of its IBVs as well as Intel to identify or rule out any additional instances of the vulnerability’s presence in the BIOS provided to Lenovo by other IBVs, as well as the original purpose of the vulnerable code.”
Lenovo said it made attempts at contacting Oleksiuk prior to posting the vulnerability online, but they had no success. Since then, they have taken the investigation into their own hands.
tags
Author
Liviu Arsene is the proud owner of the secret to the fountain of never-ending energy. That's what's been helping him work his everything off as a passionate tech news editor for the past few years.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








