Empty MS Office Documents Spark Suspicions, Bitdefender Says
Bitdefender, the innovative antivirus software provider, is warning MS Office users against a spam campaign that tricks antispam filters to allow spam freely into mailboxes. A clean Microsoft Office file is attached to these e-mails. Or so it seems!
If you recently received an odd tax return or a remittance from a bank, you might not want to open the file.
For a few days, cybercriminals have sent targeted e-mails to management departments ” other departments may receive it too. The e-mails look like a tax return, a remittance or some kind of bill from a bank, and carry a Microsoft Word (.doc) or Excel (.xls) attachment.
The e-mail isn`t stopped by antispam filters because the file itself is clean ” and how could it be dangerous? It`s empty!
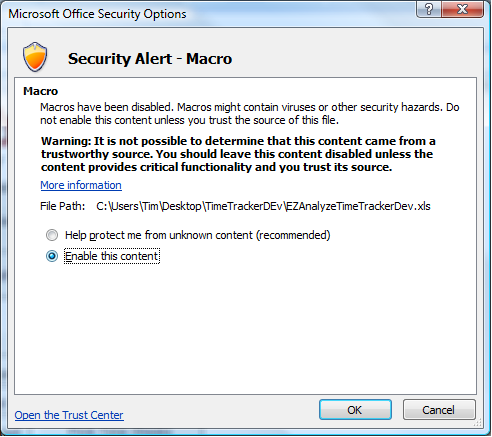
So where is the trap? It simply lies in the use of macros. Those lines of code, used in Microsoft Office, are generally used to create formulas or a repetitive task. But they also can interact with the whole Windows environment, outside Microsoft Office, and have an impact on your system.
The code in those “clean documents” is actually a command for the victim`s computer to download a piece of malware from a remote server that will execute itself automatically. The macro code is obfuscated to bypass traditional antiviruses.
The malware on the remote server is either a ransomware or an industrial espionage tool. Both are as dangerous as they look: the effect of the ransomware is immediate: it can encrypt important files of the company and ask for a ransom. The espionage tool can be even more vicious, depending on what kind of files it can access.
7000 e-mails were delivered in one day, Bitdefender researchers found. The most affected countries, by number of incidents, are Italy, France, US, UK, Australia, Canada and Germany.
How can you prevent the threat?
If you`re not used to working with macros, the warning sign at the opening of the Microsoft Office document might alert you.
A company`s network needs security from end to end and it can`t rely on a single defense. We recommend using an antivirus that proactively protects against threats, in order to block the danger before it even has the opportunity to send a command ” in this case, to prevent the macro from downloading the malware.
This article is based on information provided courtesy of Profil Technology and Bitdefender researchers.
tags
Author
Alexandra started writing about IT at the dawn of the decade - when an iPad was an eye-injury patch, we were minus Google+ and we all had Jobs.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks












