Don't Forget to Pack a USB Condom When Traveling
The only way to prevent juice jacking is to use a USB condom, which is not as crazy as it might sound. Hackers are looking for new ways to compromise people’s computers, and one way is through public USB ports.
You’re in a hurry, you’re grabbing a quick meal, and you see a USB port near the table, so you decide to charge your phone while you’re eating. It could be safe, but it could have been compromised by hackers looking to steal data or install malware on devices of unsuspecting users. This process, called juice jacking, is more common than you think.
The Los Angeles District Attorney’s Office is advising people to stay away from public USB power charging stations in airports, hotels and other locations because they could contain malware. It’s the last thing users would think about, but it’s like connecting your phone or laptop to an unsecured Wi-Fi network.
“In the USB Charger Scam, often called “juice jacking,” criminals load malware onto charging stations or cables they leave plugged in at the stations so they may infect the phones and other electronic devices of unsuspecting users. The malware may lock the device or export data and passwords directly to the scammer,” says the District Attorney office.
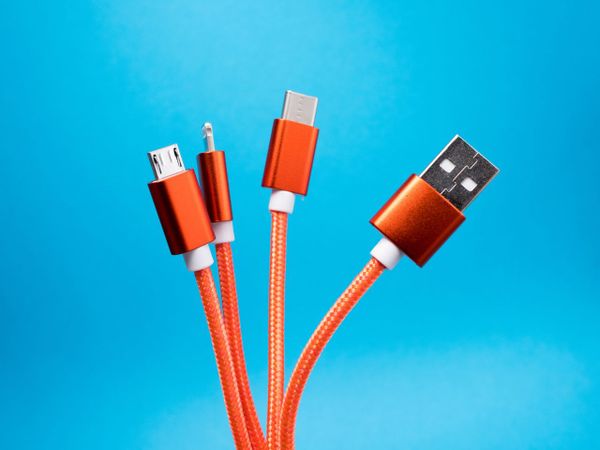
There are two ways to mitigate this problem. One would be to travel with a charger at all times, or at least use a second researchable battery. The second would be to a so-called USB condom, which is a rough but accurate description of the device.
A USB condom is a small interface that sits between your charging cable and the charging port itself. It blocks the data ports on the USB charging station, leaving only the current to pass through. It’s not overly complicated, but it works, and it’s a great way to stay safe while on the move.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







