Facebook patches serious login flaw found by Bitdefender vulnerability researcher
Have you tried creating a Facebook account under someone’s name and then use it to access his/her online accounts? Accounts you know that person manages on e-commerce or travel sites, so you could book a flight or order a smart TV on her behalf?
Ionut Cernica did exactly that. He helped Facebook patch a serious login vulnerability that allowed rogue users to access online accounts via Facebook’s social login functionality.
Ionut is 25, works as vulnerability researcher for Bitdefender and is sharpening his crypto skills at CTF competitions.
The impersonation attack
Social logins are an alternative to traditional authentication. They offer users a convenient way to sign in to their web accounts without entering their username and password. Most websites offer social login through Facebook, LinkedIn, Twitter or Google Plus.
By exploiting a vulnerability in Facebook’s login plugin, the Bitdefender researcher found a way to steal a user’s identity and gain full access to his web accounts. With one condition – for the attack to succeed, the email address of the victim must not be registered on Facebook.
To perform the test, he used two email accounts:
- [email protected] (researcher account)
- [email protected] (victim account)
He created a Facebook account with the victim’s email address.

Fig. 1 Researcher creates new Facebook account with victim email address
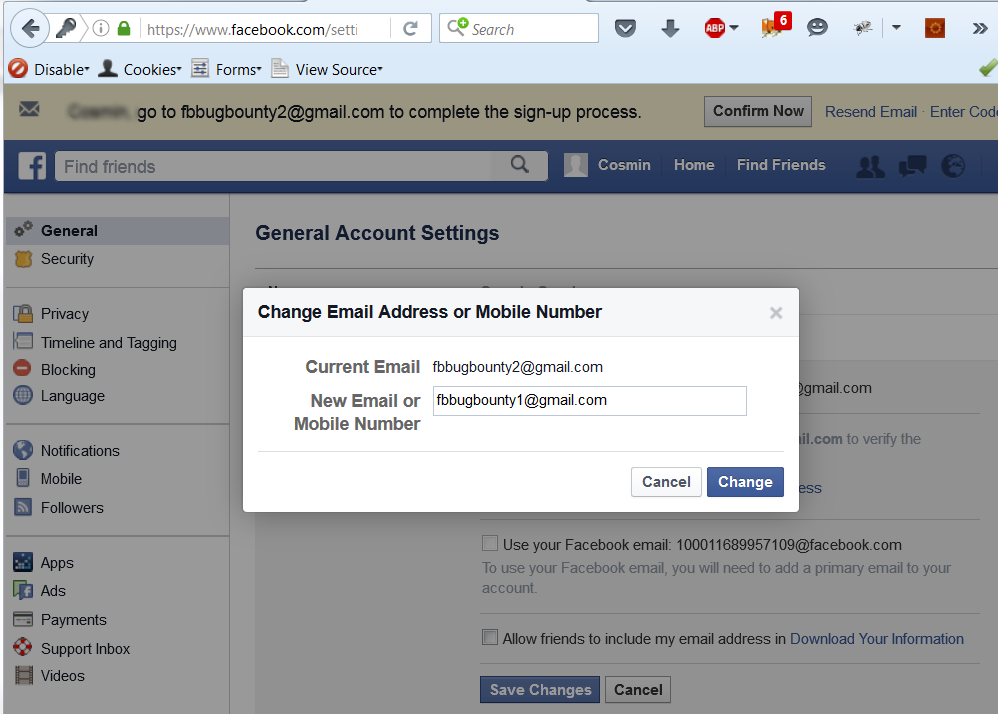
After signing up, he swapped the email address for one he controlled (in this case, [email protected] ).

Fig. 2 Researcher changes victim email address with his own
After refreshing the page, it seemed like the victim’s email address had been validated with no extra confirmation required.
When he tried to sign in via the “Facebook Login” button – with the victim’s email address – on a third-party website, he was asked to confirm his own email address, not the victim’s. Under account settings in Facebook, the victim’s address was the primary contact, even though the researcher only confirmed his personal account ([email protected]).

Fig. 3 Researcher is asked to confirm own email address
I successfully confirmed [email protected], but in the Settings page it looks like I never did,” Ionut says. “I used Facebook Login again and decided to switch the primary contact from the victim’s address to mine, then switch them again as to make [email protected] (victim account) the primary account. This is an import step to reproduce the issue.

Fig. 4 Researcher sets victim`s email address as primary contact
On another website, he used “Facebook Login” to successfully authenticate as the victim. The site matched the email address of the victim – passed to it by Facebook – to the existing account and allowed the attacker to control the account.
The identity provider – in this case, Facebook – should wait until the email address has been verified, Ionut says.
Facebook patched the security vulnerability shortly after being notified.
tags
Author
Alexandra started writing about IT at the dawn of the decade - when an iPad was an eye-injury patch, we were minus Google+ and we all had Jobs.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








