Intel Fixes Dangerous Plundervolt Vulnerability
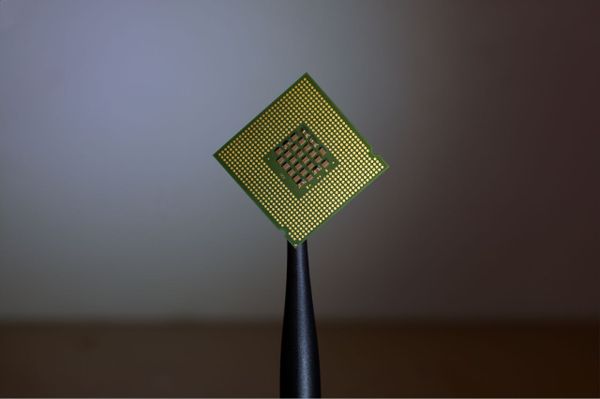
Intel has quickly released a fix for the new and already infamous Plundervolt vulnerability found in Intel 6th, 7th, 8th, 9th, and 10th generation processors, alongside Xeon Processor E3 v5 and v6, and Xeon Processor E-2100 and E-2200.
Security researchers identified a vulnerability in Intel Software Guard Extensions (Intel SGX), which is a piece of architecture embedded in several Intel processors that allows users (including the OS) to store essential code in protected enclaves, akin to a vault. Attackers obtained the cryptography key for the encrypted SGX data by lowering the voltage, compromising any system.
“A potential security vulnerability in some Intel Processors may allow escalation of privilege and/or information disclosure. Intel has released firmware updates to system manufacturers to mitigate this potential vulnerability,” states Intel”s advisory. “Improper conditions check in voltage settings for some Intel(R) Processors may allow an authenticated user to potentially enable escalation of privilege and/or information disclosure via local access.”
According to a DarkReading report, attackers undervolted the SGX systems, which allowed them to recover the AES encryption key. The patch issued by Intel disallows this for SGX, and the company promised to give users with an SGX TCB key recovery solution, which should arrive in Q1 2020.
Several universities were involved in the research, including the University of Birmingham, Technische Universität Darmstadt, University of Maryland, University of Maryland, and Tsinghua University.
The patch can only be integrated at the Bios level, which means that users will have to install Bios updates as they become available from manufacturers. Unfortunately, since Bios updates are never installed automatically, many people will remain vulnerable to this exploit until they upgrade to a new motherboard.
Each new motherboard in production right now will ship with the patch already installed, so customers should check if there is a different revision for their hardware.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







