Internet criminals outstrip hacktivists to take back dominance of the internet underworld
Organized crime, data theft, and other “old school” methods for stealing information have re-gained control over the internet underworld in the past year, shoving aside the hacktivists who had dominated the virtual landscape from 2011.
Verizon’s Data Breach Report is the best place to explore the reasons behind such a change. This report comprises millions of lost records, cataloging some 47,000 incidents of data loss. No other report covers such a huge number of breaches.
2012 was a busy year for data security. Using Verizon`s report as our guide, Let`s discuss some of the most shocking security statistics the year has to offer.
1. Internet criminals are at it again.
55% of data loss can be attributed to organized crime – more than any other potential threat from outsiders. These organized criminals are after payment cards, credentials, and bank account information.
Usually, black hat programmers themselves don’t steal money directly from these accounts. Instead they re-sell this information to a third party. A report from New York Times puts the cost at $5 – $10 per account.
This type of theft was in sharp contrast to 2011 which saw some 98% of total data loss coming from activist hackers. In the past, Hacktivist Groups like Anonymous were on an ideological mission to disrupt institutions, topping the list for total volume of data theft.
Excepting these big rare breaches, it seems there is a growing trend toward a large volume of consistent criminal activity.

Most criminals are not interested in difficult targets. They employ basic attacks against a large number of companies. Small businesses with important information but not very much protection make excellent targets. The data confirms this. Some 70% of victims are small businesses.
2. Employees are getting greedy for data.
Reported internet data theft has climbed 10% over 2011, signaling an upward trend. This theft originates within organizations themselves, in contrast to external data theft that originates from outside attackers. 92% of all attacks originated outside of the organization in 2012, down from 96% the year before.

The incidents above are not mutually exclusive, but contain one or more actions. Total data loss is shared among different actions, adding up to more than 100%. What is important to recognize is that there are proportionally more theft actions taking place from internal sources.
The depression years of 2008 and 2009 were big for internal data loss. Compared to those years, the proportion of internal to external attacks has been low. The 2012 data points to a growing trend in the number of insider data breaches and could indicate an upward trend in these type of attacks going forward.
3. Muscle heads are beating brainiacs to the money.
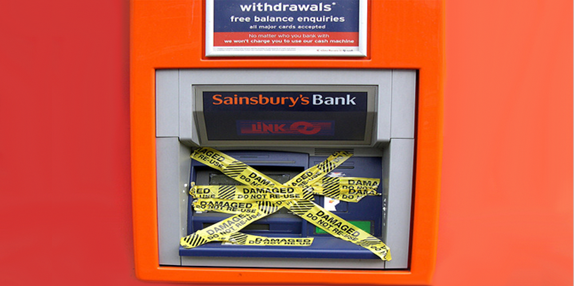
In 2012 strong arm “physical” attacks that require a physical presence to steal data made a major comeback. On-premise data theft comprises over 50% of all reported data theft worldwide.
This is in sharp contrast to 2011, where hacking accounted for 81% of the total attacks against companies. This past year was quite different.
Criminals don`t think one dimensionally. If the network is unbreakable, your windows had better be too. Criminals are well aware that many IT professionals are not prepared for a physical, on-premise break in. The statistics show that the proportion of attacks of this type rose accordingly.

A shocking spike in the amount of data loss has been occurring through non-technical theft based on human interactions with machines and people. These attack types, represented by “social” and “physical” in the graph above, were an element in some 64% of all incidents for the year.
A physical attack is any in-person method of stealing data. Examples include stealing card information at gas pumps or ATMs, or swiping a customer card through a card reader.
This is in contrast to the “social engineering” attack. Social engineering is any attack that takes advantage of a human weaknesses in security. Scam telephone calls to offices and strange email fall into this category.
(See also Yahoo Mail Blocked by Browsers in Malvertising Chain Reaction)
While the above-mentioned attacks are low tech, they are effective at compromising security. Companies need to rethink security to include the human and physical elements present in data security.
How can we prevent all this data loss?
2012 was the year of the scrappy criminal, a far cry from the advanced hacktivists on a mission to change the world by attacking large institutions in 2011.
Perhaps what makes the latest results so shocking is what it implies for the average business: criminals are looking for easy pickings, and will hack, swipe or smash their way to it.
Takeaways from this year’s Verizon report are simple: Do not think one dimensionally about your security. If your network is secure, you might consider protecting sensitive data in the event that data leaves your network. This can be accomplished through an enterprise document security solution.
If you store company computers in unlocked offices or storage areas, you may lose data to physical theft unless you increase on premise security and permit only trusted employees from accessing critical hardware.
Luckily, you now know where your security is most likely to be compromised. Because of this, you are in a position to protect it more fully than ever.
Note on word usage: In the above article the term “hacker” is used as defined by Verizon: representing attacks on data caused only by black hat programmers. A correct use of vocabulary would have been to speak about crackers instead of hackers.
Photo courtesy of: OG2T
Erik Grueter works at docTrackr, which provides document security & tracking for enterprises.
tags
Author
Erik Grueter is a marketer at docTrackr, a document security software company that empowers businesses to put the protection of important data first with powerful and analytics software.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









