Malware-Bundled Spam Run Keeps Your Boss in Carbon-Copy
When it comes to spam, cyber-crooks have always shown new and creative ways to dupe the unwary. From fake Facebook reset passwords and curriculum vitae suggestions to naked pictures with one’s teenage girl, one might think they’ve seen it all.
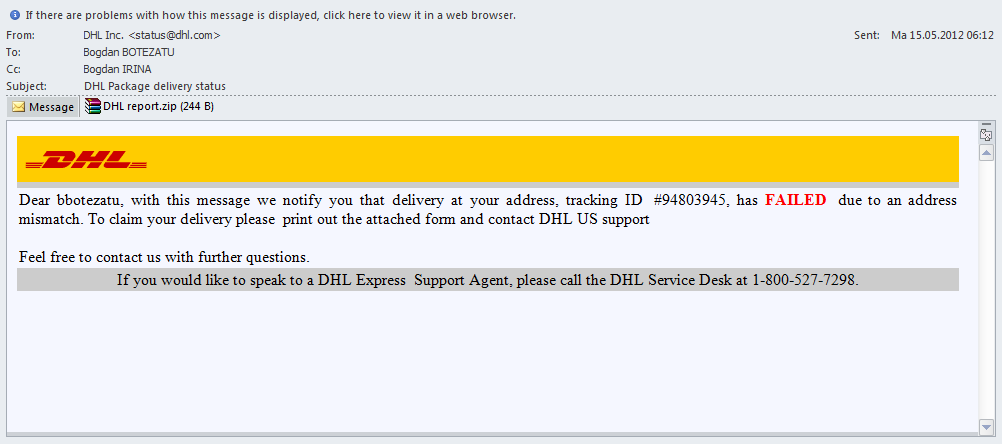
Today’s spam run comes disguised as a notification about an undeliverable parcel sent through DHL. Visually, the message has everything to really make the user believe they missed the courier package: the logo, the spoofed sender’s e-mail address and even a tracking number.
The attachment carries an executable file called dhltracking.exe and not the expected document. If opened, the attachment infects the user’s computer with a bot which is poorly detected by antivirus vendors and could allow an attacker to take control of the PC.
This usual missed parcel scam has become notorious over the past two years. What is important in this specific wave is that attackers took enough time to target corporate users and maximize damage by cc’ing the same message to an executive in the company. This “documentation” procedure is probably automated (scripts crawling the company website for key people). And then repeat the process using a different tracking code and the name of the former boss:
So, the question is: “Why is this spam run more important than others?”Â. It’s because the advanced use of social engineering allows the attacker to catch two rabbits with one e-mail. You can spam two people at once without raising suspicion. CC-ing the line manager is common practice in most businesses. Chances are the respective manager will open the message to see what the parcel notification is about. Last and most importantly, by infecting executives, the attacker may end up with some trade secrets or intellectual property at hand.
Except, of course, when spammers try to attack executives who literally set the cornerstone of the antivirus industry.
tags
Author

Bogdan is living his second childhood at Bitdefender as director of threat research.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks










