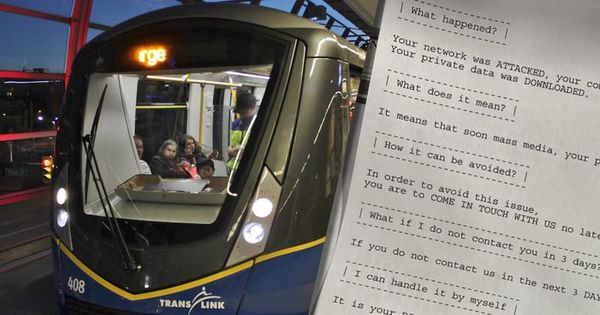
Metro Vancouver TransLink hit by Egregor ransomware attack, travellers disrupted
- Printers at TransLink churn out ransom demand from attackers
- Passengers were unable to use credit cards for travel payment
Passengers on Vancouver’s transit system were unable to use their credit and debit cards for ticket payments after the service was badly hit by a ransomware attack.
TransLink, the public transport operator in Vancouver, Canada, first indicated its IT systems were suffering problems on 1 December, when it said it was “investigating an issue.”

That “issue” turned out to be the Egregor ransomware, which hijacked TransLink’s printers and spewed out a ransom note, as documented by news reporter Jordan Armstrong in a tweeted photograph:

In the ransom message, the extortionists warned TransLink that private data was stolen from their systems and that it would begin to be published online if the company did not make contact and make a cryptocurrency payment.
It is not clear just how much money the cybercriminals want TransLink to pay for the delivery of a decryption key to undo the damage done to its data, and the promise that information will not be leaked online. Furthermore, it is unclear whether TransLink is even contemplating paying the ransom.
In a statement, TransLink CEO Kevin Desmond said the organisation took “immediate steps to isolate and shutdown key IT assets and systems in order to contain the threat” upon the ransomware’s discovery. TransLink is now “working to resume normal operations as quickly and safely as possible.”
Desmond went on to reassure customers that TransLink “does not store fare-payment data” as it uses a third party for payment processing.
It says it is limiting further comment because it has called in law enforcement to investigate the attack.
Passengers of Vancouver’s SkyTrain, meanwhile, were forced to take out money at cash machines in order to pay for their tickets, as other quicker forms of payment (such as tapping credit cards at ticket gates) were not available.
Ticket machines and fare gates are said to now be accepting card payments normally.
However, there are reports that employees’ weekly payment may be affected:
Sources tell Global News the company”s payroll operations are down. Employees will still be paid, but using a cash advance, at 65 per cent of their normal pay, but without payroll deductions, sources say.
The same Egregor ransomware haunted printers at South American retail giant Cencosud last month, churning out messages that made it hard to deny that they had suffered a cyber attack.
Not being able to buy items at a high street store is one thing, and clearly inconvenient, but ransomware impacting a city’s transport system is another entirely.
Other victims of Egregor have included Barnes & Noble and Ubisoft.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
3 in 5 travel-themed spam emails are scams, Bitdefender Antispam Lab warns
August 10, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








