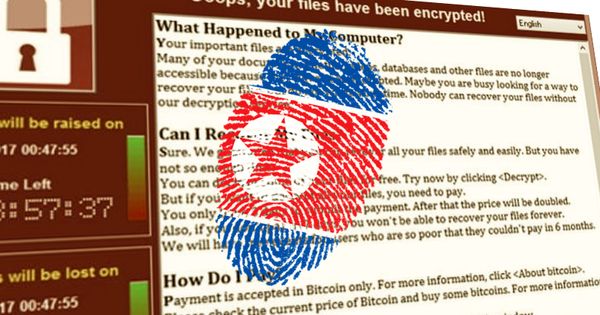
North Korea denies link to WannaCry ransomware attack
It’s understandable that people should look for someone to blame after a malware outbreak as significant as WannaCry.
Is it the fault for the NSA for discovering a security vulnerability in Microsoft’s code, and not telling Microsoft at the time? Can we blame Microsoft for shipping buggy code in the first place? Are the mysterious Shadow Brokers hacking group responsible for WannaCry, because they stole details of the exploit the NSA built to take advantage of the Microsoft flaw? Should we point fingers at the organisations who failed to patch their systems in advance of the attack?
There are arguments that all of these parties should carry some responsibility for the attack occurring, but – in my view – the ultimate blame has to lie with whoever wrote the WannaCry ransomware that leveraged the NSA’s wormable exploit to such devastating affect.
Others may have made mistakes – some serious – along the way, but the criminals who need to be brought to justice in relation to WannaCry are those who developed and released the malware.
So, who were WannaCry’s makers?
Quite frankly, we don’t know. And it’s possible we’ll never know. Despite the keen interest in law enforcement agencies around the world in identifying those responsible, it’s perfectly possible that the perpetrators may remain a mystery.
But that doesn’t mean that no-one is hunting for clues.
Last week reports emerged that some security researchers have noted curious ties between the WannaCry malware and the Lazarus hacking team that has in the past been linked to attacks against Sony Pictures, and banks in Bangladesh and South Korea.
Google researcher Neel Mehta tweeted a cryptic message highlighting similar sections of code in a threat released by the Lazarus hacking gang in February 2015, and an early version of WannaCry seen in February 2017.
Security experts at Symantec and Kaspersky confirmed Mehta’s findings, describing clear similarities in the code.
The natural conclusion is that the North Korea-linked Lazarus hacking gang was also responsible for the WannaCry ransomware attack.
But things are rarely that simple on the internet, and accurately attributing malware attacks is a minefield. After all, wouldn’t it be equally possible that someone had deliberately used code from the Lazarus gang’s previous malware to point blame in the wrong direction? Or that – just as the NSA’s exploit was being re-used by WannaCry’s creators – that the attackers were “borrowing” code from some of the Lazarus hacking team’s past endeavours?
For its part, North Korea has denied that it is in any way responsible for WannaCry – describing the allegation as “ridiculous”.
Kim In Ryong, North Korea’s deputy ambassador to the United Nations, told a press conference:
“Relating to the cyberattack, linking to the [Democratic People’s Republic of Korea], it is ridiculous”. Whenever something strange happens, it is the stereotype way of the United States and the hostile forces that kick off noisy anti-DPRK campaign deliberately linking with DPRK.”
Will we ever identify those who created WannaCry?
Consider the case of the infamous Conficker worm that – like WannaCry – exploited a Microsoft Windows vulnerability, and hit millions of computers in over 190 countries in 2008/2009.
Despite Microsoft offering a US $250,000 reward for information leading to the arrest and conviction of Conficker’s author, no-one has ever been apprehended in relation to the worm, and almost 10 years later the malware continues to spread.
If Conficker’s creators cannot be identified, what chances might there be that those behind the WannaCry ransomware might make a mistake, brag about their involvement, or have left a clue in their code which could lead to their conviction?
We shouldn’t, of course, give up hope that one day we will know for certain the truth about who created WannaCry – but it doesn’t seem a sure bet.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







