Own a Mac? You Could Be Infected with Proton RAT and Not Even Know It
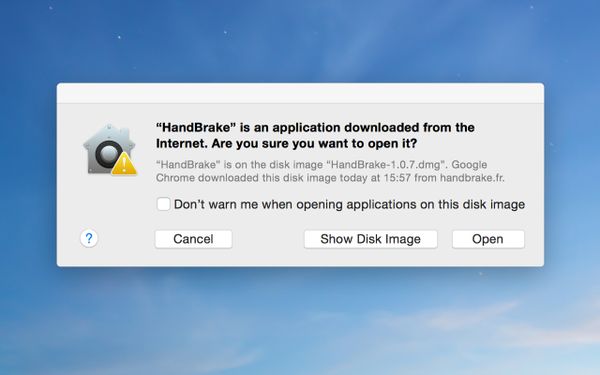
A modified version of the popular HandBrake video converter for Mac has been caught infecting Macs in the wild. The hackers breached one of the developer”s download mirrors and replaced the original DMG file with a Trojanized version for unwary users to download.
In the OS X world, there aren”t many reliable video converters you can choose from. Free converters are even scarcer. So, for Mac users looking to translate their MKVs, FLVs and WMVs into more “bearable formats,” for free, there are only a handful of choices – chief among them, HandBrake.
Originally developed by the same people behind the Transmission project, HandBrake has become the go-to app for converting video on a Mac. Being such a popular tool, it has also caught the eye of hackers looking to get their mitts on Mac users” data. Such was the case this past weekend when the HandBrake team was forced to warn users against downloading the latest version of its software.
“Trojanized” HandBrake
“Anyone who has downloaded HandBrake on Mac between [02/May/2017 14:30 UTC] and [06/May/2017 11:00 UTC] needs to verify the SHA1 / 256 sum of the file before running it […] to verify their system is not infected with a Trojan,” the team’s advisory reads. “You have 50/50 chance if you’ve downloaded HandBrake during this period.”
The respective Trojan is a new breed of OSX.PROTON dubbed OSX.Proton.B. Proton is a Remote Access Trojan (RAT) designed specifically to target Macs. It was developed a few months ago and sold for a handsome sum of bitcoins (reportedly for 40 BTC, or roughly $65,000) on the underground Russian Internet.
Signed with a special signature that only legitimate Apple developers can get their hands on, the malware can get past Apple”s “Gatekeeper” security defenses. From there on, Proton RAT can:
- record keystrokes
- upload and downloading files to and from a remote location
- control the webcam
- allow an attacker to connect remotely to your Mac
- display a custom-made dialog prompting the user to enter user names and passwords, credit card information, etc.
- access the user”s iCloud account
- bypass two-factor authentication
In short, Proton RAT can wreak havoc once it makes its way into your machine.
How to detect OSX.Proton.B
There are two ways to confirm whether you”ve had the misfortune of installing the hacked version of HandBrake.
Method 1:
First, you should check for a process called “Activity_agent” in Activity Monitor. Simply hit CMD + Space Bar to launch Spotlight, type in Activity Monitor and hit Return/Enter. If “Activity_agent” shows up as a process in the Activity Monitor window, you are infected.
Method 2:
Another way to diagnose your system is to compare the HandBrake DMG”s checksum against the checksums below. Follow these instructions to do that.
SHA1: 0935a43ca90c6c419a49e4f8f1d75e68cd70b274
SHA256: 013623e5e50449bbdf6943549d8224a122aa6c42bd3300a1bd2b743b01ae6793
If it is any of these two, according to the HandBrake team, you are infected.
How to remove OSX.Proton.B
If you were infected, you can take some steps to mitigate the risks listed above.
Launch “Terminal” on your Mac application and run the following commands:
launchctl unload ~/Library/LaunchAgents/fr.handbrake.activity_agent.plist
rm -rf ~/Library/RenderFiles/activity_agent.app
If the proton.zip archive shows up in the ~/Library/VideoFrameworks/ folder, remove the folder entirely and then remove any “HandBrake.app” installs you may have on your Mac”s drive. To re-download the clean version of the app, use the primary download mirror on the official HandBrake website.
BitDefender Antivirus for Mac automatically detects Proton RAT, and other pieces of malware it may have subsequently dumped on your system. Infected users are also advised to change all the passwords sitting in their OS X KeyChain, “or any browser password stores,” according to the HandBrake team.
At this point, anyone attempting to install the malicious file should already be protected by Apple”s Xprotect mechanism.
tags
Author
Filip has 15 years of experience in technology journalism. In recent years, he has turned his focus to cybersecurity in his role as Information Security Analyst at Bitdefender.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







