Popular Twitter Hashtag Fills up Social Engineers` Data Base
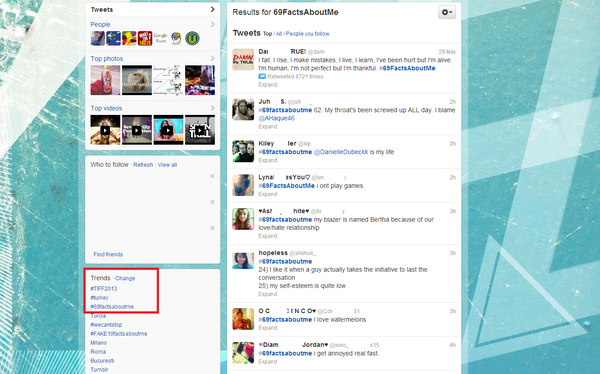
One of Twitter`s most popular hashtags may become a strong social engineering resource. As users share personal information with complete strangers, #69factsaboutme will increasingly be used by scammers for nefarious purposes. Over 200,000 tweets were already posted under the hashtag at the time of publishing.
“I have two houses that I live in,” one user said. “I think BoyzIIMen is the greatest musical group of all time,” tweeted another. These are just a few of the personal details and interests Twitter users commonly share on #69factsaboutme. The allure of the increasingly popular hashtag stems from people`s willingness to talk about what they like the most ” them.
 Users share information such as their best friends` names, their interests, their pet`s name and their mother`s maiden name. These can all be easily gathered by cyber-criminals to create complete profiles for targeted attacks, to guess passwords and to steal identities.
Users share information such as their best friends` names, their interests, their pet`s name and their mother`s maiden name. These can all be easily gathered by cyber-criminals to create complete profiles for targeted attacks, to guess passwords and to steal identities.
At the end of May, #69factsaboutme gained a spot in the 10 trendiest topics in the US, according to TweetTrendings. With the rising popularity of such hashtags, social engineers will soon leave the urban legendary dumpsters to search for valuable information exclusively online.
Compared to hackers with authentic computer skills, social engineers don`t need to know advanced code to cash their pay check. They often exploit users` natural helpfulness and vanity, as well as their willingness to make their lives public. Social networks are among the most efficient methods they use to gather information for fraud or targeted hacking. Social engineering also relies on the fact that people are careless with personal information they expose on the Internet.
At the same time, social engineering forms part of many types of exploits. From malware writers who persuade us to run e-mail attachments, to phishers who trick us into sending them our credit card details, social engineering is the Ëœ`must have” of most cyber-attacks.
Twitter`s 69factsaboutme isn`t the only place where social engineers may find information already conveniently grouped. Facebook`s Graph Search can also be a powerful method of capturing and correlating information for targeted fraud and phishing.
In May, Twitter announced two-factor authentication and included mobile phones in the verification processes, after a series of high-profile hacks.
Tips and tricks:
Protect your personal information – never underestimate its value.
Train your friends and family to become aware of personal details they share online.
If you`re a parent, talk to your kids about the importance of online privacy and the risks they are exposed to when sharing information with people they don`t know in real life.
Revise the messages you have posted on social networks and check if you didn`t share too much personal data.
Search your name and your friends` names in people search engines and on social networks. Try to come up with a profile that gathers as many details as possible and imagine how a cyber-criminal may use such information.
Don`t overdo it! You can have fun with online sharing, as long as you`re careful.
P.S.: Not all information shared via #69factsaboutme has value for social engineers. They will most probably not use tweets such as “I’m single because no one is worthy of me. Jk I’m single because I’m a loser and no one likes me.”
All product and company names mentioned herein are for identification purposes only and are the property of, and may be trademarks of, their respective owners.
tags
Author
Bianca Stanescu, the fiercest warrior princess in the Bitdefender news palace, is a down-to-earth journalist, who's always on to a cybertrendy story.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








