Ransomware extorts Los Angeles school to the tune of $28,000
Blackmailers have claimed another scalp, extorting US $28,000 from a school hit by a ransomware attack.
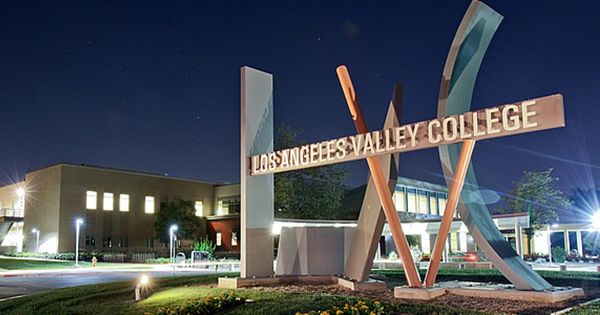
Los Angeles Community College District (LACDD) agreed to pay the hefty ransom demand to criminals who successfully infected the network of Los Angeles Valley College (LAVC) in a ransomware attack on December 30th, 2016.
It’s always disappointing, of course, to hear that a ransomware attack has again resulted in a payout for criminals, but it’s understandable how some organisations might have to make a difficult pragmatic decision if it has few other options open to it.
That certainly seems to be the case with LAVC, which in an FAQ about the incident, explained that it felt it was unlikely to be able to recover its data without paying the sizeable ransom:
“It was the assessment of our outside cybersecurity experts that making a payment would offer an extremely high probability of restoring access to the affected systems, while failure to pay would virtually guarantee that data would be lost.”
College president Erika Enrijonas explained how the unnamed ransomware disrupted computer activity, as well as internet access, email and voicemail systems. As with the majority of ransomware attacks, there is nothing to indicate that the college was deliberately targeted.
No mention is made as to whether the college had secure backups which it could use to recover its systems (and thus avoid paying the criminals who had attacked it). Instead, the LAVC’s FAQ describes how it was insured against cybersecurity incidents:
“The District has a cybersecurity insurance policy to address these specific types of cyber intrusions and it was activated during this incident. While much time will pass before this matter is resolved, we have already availed ourselves of the resources provided by the policy, including assistance of cybersecurity experts.”
After paying the ransomware attackers US $28,000, the college received a decryption key to unlock their encrypted data. That, of course, is not the end of the story – as Enrijonas admits:
“The process to ‘unlock’ hundreds of thousands files will be a lengthy one, but so far, the key has worked in every attempt that has been made.”
Ransomware attacks are on the rise, and a disappointing number of organisations are finding themselves with precious few options other than to reward the criminals who attacked them.
Even police departments are reported to have given in to online criminals and paid cash to get their data back after being hit by ransomware.
No business wants to give in to blackmail and pay an extortionist. What Los Angeles Valley College decided was that it didn’t have any other option. A sensible secure backup policy and adequate defensive measures might have opened opportunities to avoid paying the ransom.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
3 in 5 travel-themed spam emails are scams, Bitdefender Antispam Lab warns
August 10, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







