Rookie Phishing Attempt Hits Black Hat Attendees; 7,500 Participants Targeted
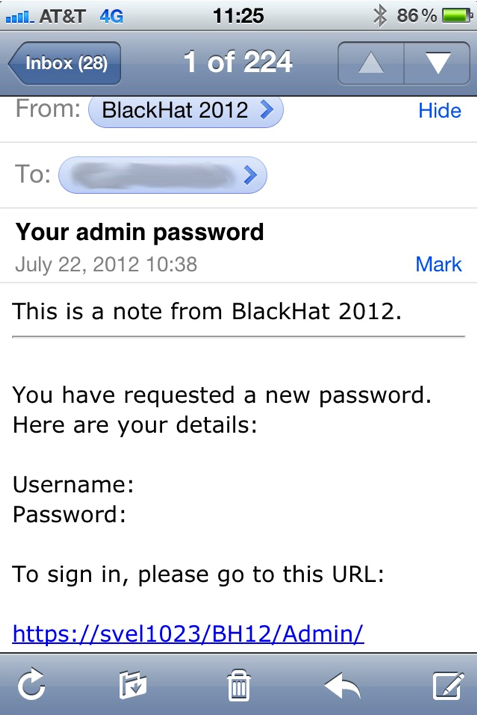
A password reset e-mail apparently sent by a Black Hat volunteer reached the inbox of approximately 7,500 security experts in what appears to be a very basic attempt to collect their usernames and passwords.
The maladroit, yet malicious message actually claimed to provide recipients with new credentials they had allegedly requested. As the sender appeared to have forgotten to include the data proper, it was expected that targeted participants would log in by accessing an embedded link.
Source: https://www.blackhat.com/html/latestintel/07222012-USA-Reg-Email.html
Reports on the incident noted that there were several clues about the message being a fake that Black Hat participants probably picked up in a glimpse: the credentials were supposed to have been provided in plain text, the embedded link led to a web site other than Black Hat`s, plus the sender`s e-mail address – itn-international.com- indicated that someone other than Black Hat had access to participants` contact details.
Black Hat officials took quite a humorous turn in their apology note: “We love to tease people that your systems need to be ready to hold their own if joining the Black Hat network. In this frame of mind, the community very correctly expected a prank or act of malice.” Nevertheless, they alluded to being aware of the likelihood of third parties` security vulnerabilities: “The far more concerning thought would be how is ANYONE other than Black Hat emailing the registered delegates for the 2012 show? Some data is shared on a need-to-know basis with some key partners, one of which is ITN who is handling our on-site registration and check-in systems at the show this year.”
Fortunately, the incident did not cause any real damage, as none of the participants` credentials were stolen.
“Our most valued assets at Black Hat are our delegates and their privacy. We work very hard to maintain that. We want everyone to come to Black Hat to learn and enjoy their time without fear of having their personal or professional information compromised. We are happy to report there are no signs of compromise. The email this morning was an abuse of functionality by a volunteer who has been spoken to. This feature has since been removed as a precautionary measure”, concluded the blog post signed by Trey Ford, general Manager, Black Hat.
tags
Author
Ioana Jelea has a disturbing (according to friendly reports) penchant for the dirty tricks of online socialization and for the pathologically mesmerizing news trivia.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









