Russian Hackers Promise Anti-Government Software, Deliver Kelihos Trojan Instead, Bitdefender Warns
A self-proclaimed hacker community from Russia installs data-stealing malware on users’ machines by pretending the software was designed to attack Western governments and the US, according to antivirus software company Bitdefender.
With the Ukrainian conflict in mind, hackers have crafted ingenious spam messages that help them deliver the Trojan to those who support the Russian “cause” and dislike measures taken against the country. Users who click the malicious links are unwillingly joining the botnet and spreading the malware further.
The Trojan drops three clean files used to monitor traffic (WinPcap files npf.sys, packet.dll, wpcap.dll), and is capable of mining sensitive browser data, internet traffic and other personal information.
“We, a group of hackers from the Russian Federation, are worried about the unreasonable sanctions that Western states imposed against our country,” malicious messages read, according to Bitdefender’s Russian-speaking antispam researchers. “We have coded our answer and bellow you will find the link to our program. Run the application on your computer, and it will secretly begin to attack government agencies of the states that have adopted those sanctions.”
 After clicking the links, victims download an executable file known as Kelihos. The Trojan communicates with the command and control center by exchanging encrypted messages via HTTP to retrieve further instructions.
After clicking the links, victims download an executable file known as Kelihos. The Trojan communicates with the command and control center by exchanging encrypted messages via HTTP to retrieve further instructions.
Depending on the type of payload, Kelihos can do any of the following:
- Communicate with other infected computers
- Steal bitcoin wallets
- Send spam emails
- Steal FTP and email credentials, but also login details saved by the browsers
- Download and execute other malicious files on the affected system
- Monitor traffic for FTP, POP3 and SMTP protocols
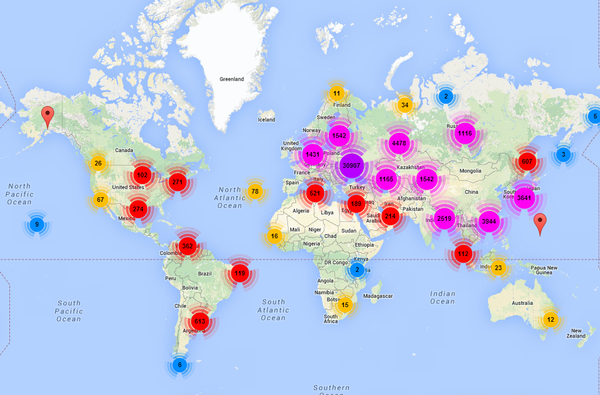
The Bitdefender Labs analyzed one of the recent malicious spam waves and noticed that all the .eml files lead to setup.exe links, with 49 unique IPs. Oddly enough, over 40 per cent of the infected servers are in Ukraine, according to a more detailed analysis by the Bitdefender Labs.
 Some might be servers specialized in malware distribution or other infected computers that became part of the Kelihos botnet,” Bitdefender Virus Analyst Doina Cosovan said. “It is somehow ironic that most of the infected IPs are from Ukraine. This either means that computers in the country were also infected, or that Ukraine itself is where the distribution servers are located in.”
Some might be servers specialized in malware distribution or other infected computers that became part of the Kelihos botnet,” Bitdefender Virus Analyst Doina Cosovan said. “It is somehow ironic that most of the infected IPs are from Ukraine. This either means that computers in the country were also infected, or that Ukraine itself is where the distribution servers are located in.”
Bitdefender blocks both the malicious spam wave and the Kelihos Trojan, protecting its users’ computers from infection.
 To convince many users of their authenticity, the Russian hackers added some marketing “glitter” on their messages. They claim their program works silently, using no more than 10 to 50 megabytes of traffic per day, and takes almost no CPU time.
To convince many users of their authenticity, the Russian hackers added some marketing “glitter” on their messages. They claim their program works silently, using no more than 10 to 50 megabytes of traffic per day, and takes almost no CPU time.
“After rebooting your computer, our program will terminate its activities, and if you want to – you can run it again,” spam e-mails also read. “If necessary, turn off of your antivirus at that time.”
Of course, turning off your security solution is not advisable. Instead, keep it installed and updated, just like your other software and operating system because malicious programs usually take advantage of vulnerabilities found in non-updated software.
Also known as Hlux, the Kelihos botnet was discovered four years ago. It is mainly involved in the theft of bitcoins and spamming. The botnet has a peer-to-peer structure, where individual nodes can act as command-and-control servers for the entire botnet, increasing its longevity.
In January 2012 a new version of the botnet was discovered, and Microsoft pressed charges against a Russian citizen who was the alleged creator of the Kelihos Botnet’s sourcecode.
All product and company names mentioned herein are for identification purposes only and are the property of, and may be trademarks of, their respective owners.
This article is based on spam samples provided courtesy of Bitdefender Spam Researcher Adrian MIRON and the technical information provided by Bitdefender Virus Analyst Doina COSOVAN and Alexandru MAXIMCIUC.
tags
Author
Bianca Stanescu, the fiercest warrior princess in the Bitdefender news palace, is a down-to-earth journalist, who's always on to a cybertrendy story.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








