The insider threat highlighted by Hacking Team and Ashley Madison hacks
Many of us spend a lot of time worrying about external hackers, spammed-out malware and internet intrusions – but sometimes the instigators of an attack against your business can be much closer to home.
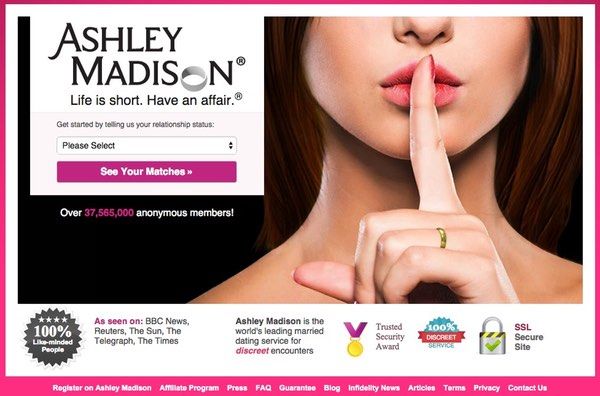
Today, headlines are filled with news that hackers have apparently broken into adultery site Ashley Madison, and are threatening that unless the website is closed down, a database containing the personal information of 37 million users will be released.
Source: ashleymadison.com
Noel Biderman, the CEO of Avid Life Media which runs the Ashley Madison website, told security blogger Brian Krebs that the attacker might be someone who was previously contracted to work on the company’s IT systems:
“We’re on the doorstep of [confirming] who we believe is the culprit, and unfortunately that may have triggered this mass publication,” Biderman said. “I’ve got their profile right in front of me, all their work credentials. It was definitely a person here that was not an employee but certainly had touched our technical services.”
Whether that’s true or not, I don’t know.
It would certainly be surprising for any company which has been hacked to be able to assert with confidence that it knew who had hacked its systems after such a short period of time. And it’s worth remembering that even if a past contractor’s login details had been used, that doesn’t necessarily mean that it was that ex-contractor who accessed the system.
But it does make sense that the company investigate whether the hack could have been an “inside job”, rather than the work of remote hackers who had no special knowledge of the firm.
Interestingly, a similar investigation is taking place right now into the controversial goings-on at Italian firm Hacking Team.
Reuters is reporting that Italian police are investigating former employees of the troubled spyware company Hacking Team, in connection with the massive hack it recently suffered.
As was reported widely last week, Hacking Team – a firm which specialises in helping governments and intelligence agencies use malware to spy on their citizens – suffered a hack which saw its email archive spill out onto the web, internal documents and sensitive contracts exposed, and source code stolen.
Source: Hacking Team Twitter account
As a consequence, a number of new zero-day vulnerabilities exploited by Hacking Team products have been released into the wild, forcing the likes of Oracle and Adobe to update their Java and Flash software with security patches.
According to Reuters, Hacking Team boss David Vincenzetti filed a complaint back in May, accusing six former workers of revealing some of the company’s sensitive source code. Prosecutors in Milan are said to have now combined that investigation into the main investigation regarding who hacked Hacking Team.
Both of these hacks raise an important issue that all companies need to face. Regardless of how you are going to protect your business from external hackers and internet attacks – what are you doing to defend your organisation from your staff and contractors?
Workers inside your company have special privileges – they’re expected to access files that aren’t available to the outside world, log into internal email systems and perhaps even connect to your servers remotely while working from home or on-the-road.
If an employee or contractor turns rogue, you need to do whatever is possible to reduce the chances of them taking sensitive information with them, and ensure that any systems they were previously allowed to access can no longer be accessed. Even if there is no indication that a worker has got a chip on his or her shoulder, or is joining a business rival, then it should be a matter of course to ensure that systems remain secure after they have left.
One obvious example is ensuring that any passwords known to that user are wiped when they are no longer employed by your company, or are working on that particular project.
It’s too early to know whether the Hacking Team and Ashley Madison hacks were the work of, or were assisted by, insiders. But it’s clear that many companies are doing a very poor job of securing systems from their former staff and contractors.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









