Trojan.Obad.A Gets Administrator Privileges and Manages Your Device for You
A new variant of Android malware is making its rounds in the wild, wreaking havoc among users and taking complete control over the infected smartphone.
Once launched, the sophisticated Android.Obad.A, lurking inside an innocent-looking application, asks users to give it administrative privileges enabling the Trojan to manage the device from deep within the system.
Android.Obad.A is equipped with an array of malicious functions, including sending SMS to premium-rate numbers, entering commands in the device console remotely, downloading further malicious code to install on the compromised handsets or even infect other devices via Bluetooth.
The malware abuses a bug in DEX2JAR, a software used by reverse-engineers to turn APK files into JAR files, as well as a vulnerability in the way Android reads the AndroidManifest.xml file to compromise any attempts of code analysis, either static or dynamic.
In order to hide its presence on the device and make removal nearly impossible, Android.Obad.A exploits a previously unknown vulnerability in the Android ecosystem to conceal its presence in the Device Administrator lists. Shortly put, an application can’t be uninstalled until its Device Administrator privileges are revoked, which is impossible for an unlisted application.
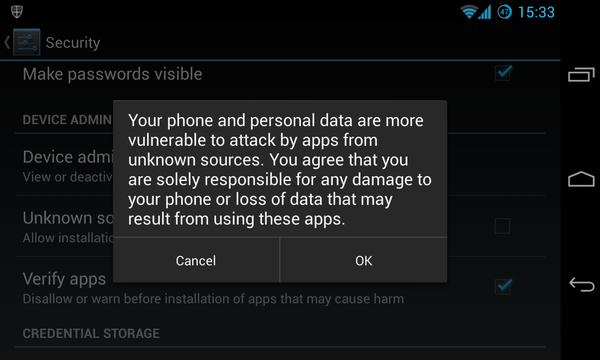
Fortunately for most Android users, the malware only seems to be delivered via third-party Android markets. As a precautionary measure, all Android devices are distributed with the option to install applications from “unknown sources” disabled by default. And when trying to enable it, the user is shown the following warning:
Users in some regions are however forced to use unsanctioned Play stores. If this is not the case for you, make sure you keep this option disabled.
To avoid getting infected with Android.Obad.A, check the configuration of your handset by going through the following steps:
- Go to SETTINGS
- Go to SECURITY
- Make sure the “UNKNOWN SOURCES” is NOT checked
Other signs that may indicate the presence of malware on your handset:
- Sudden drop in the battery life of your device, in the absence of battery-straining activities
- Suspiciously costly phone or/ and data plan bills
- Sudden performance issues are indicative of malicious activities, especially if there were no changes in your interaction routine with the device
Apart from carefully scrutinizing every permission required by an Android app, installing mobile security software can prove vital for the protection of your mobile device and personal data from any type of malware.
tags
Author
A blend of product manager and journalist with a pinch of e-threat analysis, Loredana writes mostly about malware and spam. She believes that most errors happen between the keyboard and the chair.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









