VTech toymaker hacked - millions of families have their personal info exposed
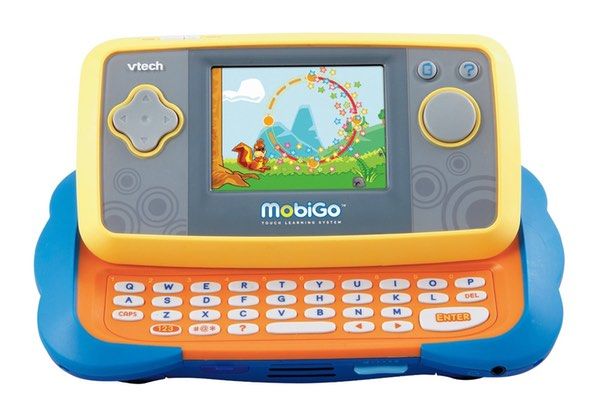
VTech, a leading maker of electronic learning toys, has suffered a serious security breach, with hackers accessing a database containing information about customers and their children.
As a result, data including users’ email addresses, home addresses, security questions and answers, children’s names and dates of birth, and easily-reversible passwords have been accessed.
An article on Motherboard explains, the hacker initially contacted security reporter Lorenzo Franceschi-Bicchiera, saying that they had managed to access VTech’s database by using an SQL injection attack.
The hacker says that they have no plans to exploit the stolen data, or publish it publicly, but if is true that the data was accessible via a rudimentary SQL injection attack – there is no guarantee that other more maliciously-minded hackers might not have stolen the data beforehand.
Security researcher Troy Hunt, who assisted Motherboard with its investigation into the breach, examined the stolen data in great detail, and documented a number of security failings on VTech’s part.
Hunt discovered that there were over 4.8 million unique email addresses in the database, alongside passwords that were not stored in plaintext – but were still trivial to crack. Furthermore, Hunt discovered that users’ secret questions and answers were being held in plaintext.
An obvious concern is that not only might a malicious party be able to determine VTech customers’ passwords and attempt to use them to unlock other online accounts, but the “secret” answers might also help with the compromise of – for instance – webmail or banking accounts elsewhere too.
A further blow to VTech’s credibility when it comes to security is its failure to use SSL to encrypt information (such as passwords) when transmitted – opening opportunities for malicious hackers to steal data with ease.
But perhaps what is most disturbing is that the stolen data includes information about customers’ children.
As Hunt describes, parents who used VTech’s Learning Lodge app store to download apps, games and ebooks to their VTech products, were encouraged to create and links profiles for their children – including names, gender, and dates of birth. In all, there are over 227,000 children’s records in the hacked database.
VTech customers have been sent an email by the Hong Kong-based company, which informs them about the security breach but fails to mention that details of children were also at risk.
More up-to-date information, which acknowledges that children’s information has also been exposed, was posted today in a press release on VTech’s website.
At the time of writing, while it attempts to harden its security, VTech has suspended access to the Learning Lodge website:
Hopefully it’s obvious that if your’e using the same password on multiple sites that now is a great time to break out of that habit – and start using unique credentials for each online account you have. My advice is to use a password manager to remember complex, unique passwords on your behalf.
But another piece of advice may be to start thinking twice about whether you really *need* to give correct information for each service which asks for it. For instance, was it really necessary to tell VTech the real dates of birth for your children? Sometimes lying can be a more sensible course of action.
If there’s any luck in the world, the hacker will be true to their world and not publish any of the stolen data. With luck, no other hackers will have stumbled across the security weaknesses on VTech’s website, and won’t have made copies of the data, and won’t be attempting to find a way to criminally exploit them.
But it’s not good enough that we should have to cross our fingers and hope for good luck when it comes to trusting manufacturers that they are not being reckless with our family’s personal information.
Too many companies aren’t putting security and privacy at their core, and are unnecessarily putting many of us at risk.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









