What is cyberstalking?
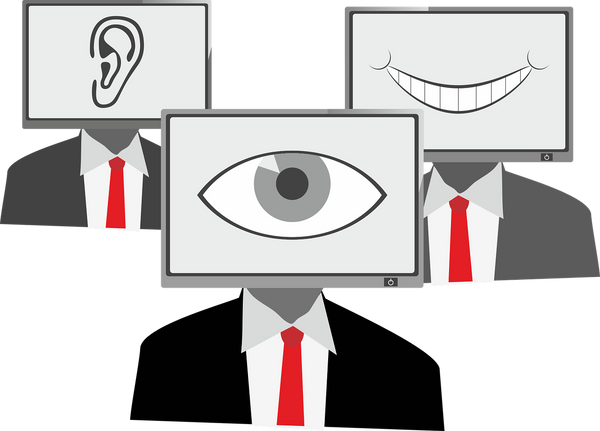
Unlike physical stalking, which takes place in the real world, cyberstalking is defined as stalking or harassment carried out in the digital world via social media, email, chat rooms, forums and other online channels. The online stalker can be a complete stranger or someone you know or have met in the past.
Around 30% of Internet users in the U.S. have experienced some invasion of privacy according to a 2016 study. The loss of privacy or control over personal information is considered a form of online harassment. The report also emphasized that most victims of cyberstalking suffered theft of sensitive information, causing personal, professional or financial damage.
How does a cyberstalker operate?
• Catfishing is most common on social media websites or dating apps. In this scenario, the cybercriminal creates fake profiles to get close to you and obtain photos or other private information.
• Denial of access – this practice includes message bombing, preventing access to online accounts by misuse of online reporting tools. By constantly flooding your phone, email or chat window, the cyberstalker can limit access to phones or other communication platforms.
• Doxing – refers to the practice of researching and posting private or identifiable information (PII) about an individual or organization online without their consent.
• Stalkerware – cyberstalkers use spying software to monitor a victim”s messages, call information and GPS locations. Such spyware can range from Trojans to keyloggers that run on a victim”s smartphone, computer or tablet. Information gathered may include passwords, credit card information, emails and text messages, photographs or any other PII that can be used for impersonation attacks and identity theft.
• Monitoring location check-ins and geotags – Posting your location online can provide a criminal with the means needed to physically track you. Another way to track your whereabouts is by checking the geotags of your pictures. Every photo is embedded with a geotag that shows where and when a photo was taken.
• Webcam hijacking – a preferred way for cybercriminals to invade your privacy is to trick you into downloading malware-infected files on a device. If successful, they can access your webcam and monitor your every move.
How can you protect yourself from cyberstalking?
As previously mentioned, the cyberstalker is not always an acquaintance. Beyond live chat harassment, flaming (online verbal abuse), threatening, spamming and defamation, online stalkers may actually be after your personal information that can be used in crimes including, identity theft, impersonation and fraud. Since cyberstalkers rely on the anonymity of the Internet, it can be very hard to track them down. In some cases, victims are unaware they are being stalked. Some of the best practices that you can adopt to limit cyberstalking include:
• Review and limit the information you post and social media platforms
• Change and update your passwords regularly
• Enable multi-factor authentication for your accounts
• Use a VPN that can help protect your personal information
• Avoid connecting to untrusted WiFi networks
• Avoid accessing shady websites and downloading files from untrusted sources and individuals
• Use a security solution on all of your internet-enabled devices, such as computers, phones and tablets
• Keep an eye on your Inbox for phishing emails
Anyone can be a victim of cyberstalking. It”s always a good idea to be aware and limit your online presence as much as possible. If you or a family member have fallen victim to a cyberstalker, the best course of action is to gather all evidence possible and contact your local authorities.
Legislation on cyberstalking differs from country to country. In the United States, most states have laws against this type of online behavior or harassment. If found guilty of cyberstalking-related crimes, sentences can range from years in prison to hefty fines.
Social media platforms, such as Facebook, advise victims to immediately block the person harassing them and report the account for misuse.
tags
Author
Alina is a history buff passionate about cybersecurity and anything sci-fi, advocating Bitdefender technologies and solutions. She spends most of her time between her two feline friends and traveling.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








